1. Identifying the “Big Three” Logs
To detect attacks, you need to monitor three specific locations:
- NGINX/Apache Access Logs: Shows every request made to the server (who, when, and what).
- NGINX/Apache Error Logs: Shows failed requests, 403 Forbidden errors, and server-side crashes.
- Auth Logs (
/var/log/auth.log): Shows SSH login attempts andsudousage.
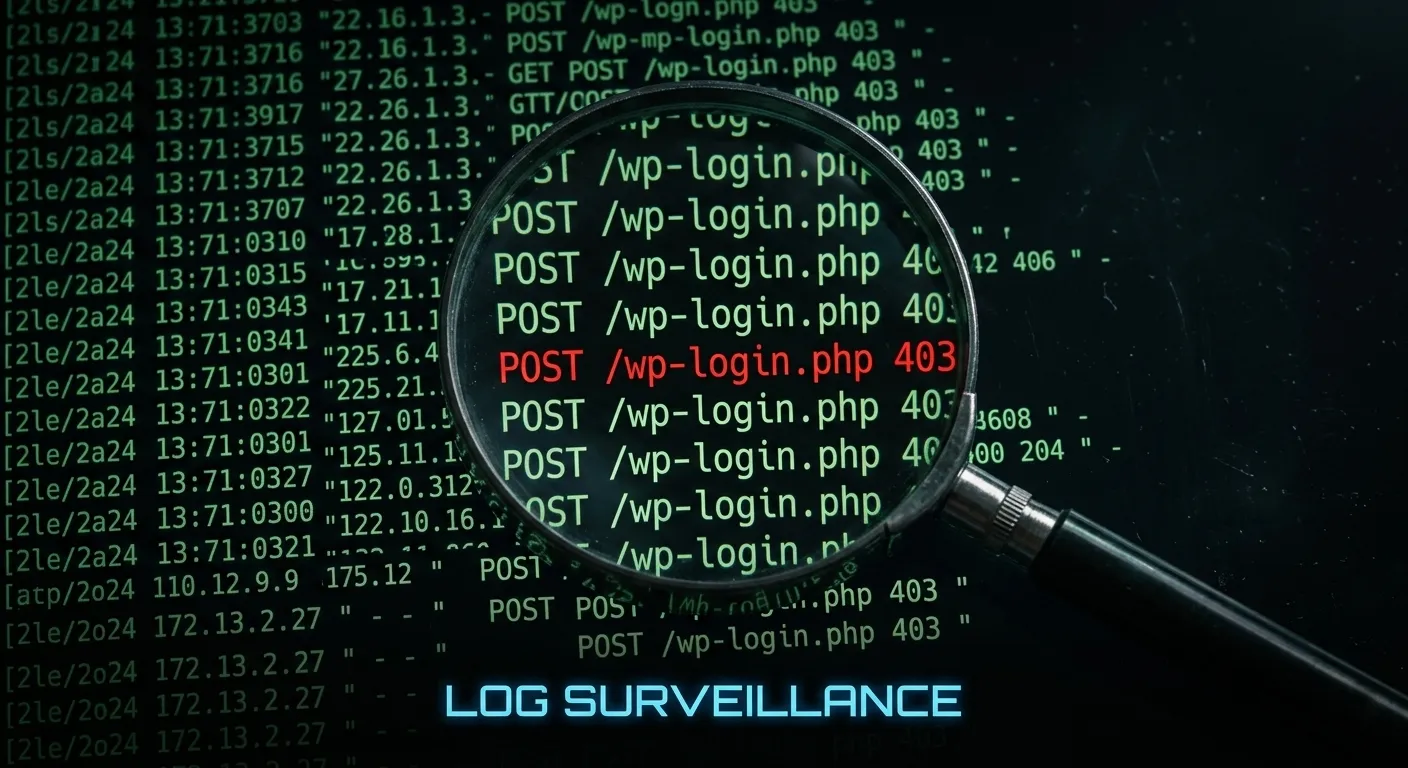
2. Detecting Brute Force via Access Logs
Automated bots hit your login endpoints repeatedly. You can spot them by looking for a high frequency of POST requests to wp-login.php or xmlrpc.php.
- The Command: “`bash grep “POST /wp-login.php” /var/log/nginx/access.log | cut -d’ ‘ -f1 | sort | uniq -c | sort -nr | head -n 10
*This command lists the top 10 IP addresses trying to brute-force your login.*
3. Spotting Vulnerability Scanners
Attackers use tools like WPScan to look for outdated plugins. You’ll see a surge of 404 or 403 errors in your logs as the bot tries to access directories that don’t exist.
- What to look for: Rapid requests for paths like
/wp-content/plugins/wp-config-backup/or/wp-content/plugins/revslider/. - The Red Flag: A single IP address generating hundreds of
404errors in a few seconds is a bot mapping your site for exploits.
4. Detecting SQL Injection Attempts
SQL injection attacks often leave traces in the query strings of your access logs. Look for suspicious characters like UNION, SELECT, or DROP.
- The Command:Bash
grep -E "union|select|insert|update|delete|drop" /var/log/nginx/access.log - The Fix: If you see these, ensure your database user has restricted permissions and that you are using a Web Application Firewall (WAF) like Cloudflare to block these payloads at the edge.
5. Monitoring SSH Unauthorized Access
If you are running a VPS, your SSH port is likely being hammered.
- The Command:Bash
grep "Failed password" /var/log/auth.log - The Strategy: If you see “Failed password for root,” it’s time to disable root login and move SSH to a custom port immediately.
6. Tools for Real-Time Monitoring
Don’t just read static files; watch them live.
- Tail: Use
tail -f /var/log/nginx/access.logto see traffic in real-time. - GoAccess: A terminal-based (or web-based) visualizer that turns your raw logs into a real-time dashboard. It’s lightweight and perfect for developers.